What is the Darknet?
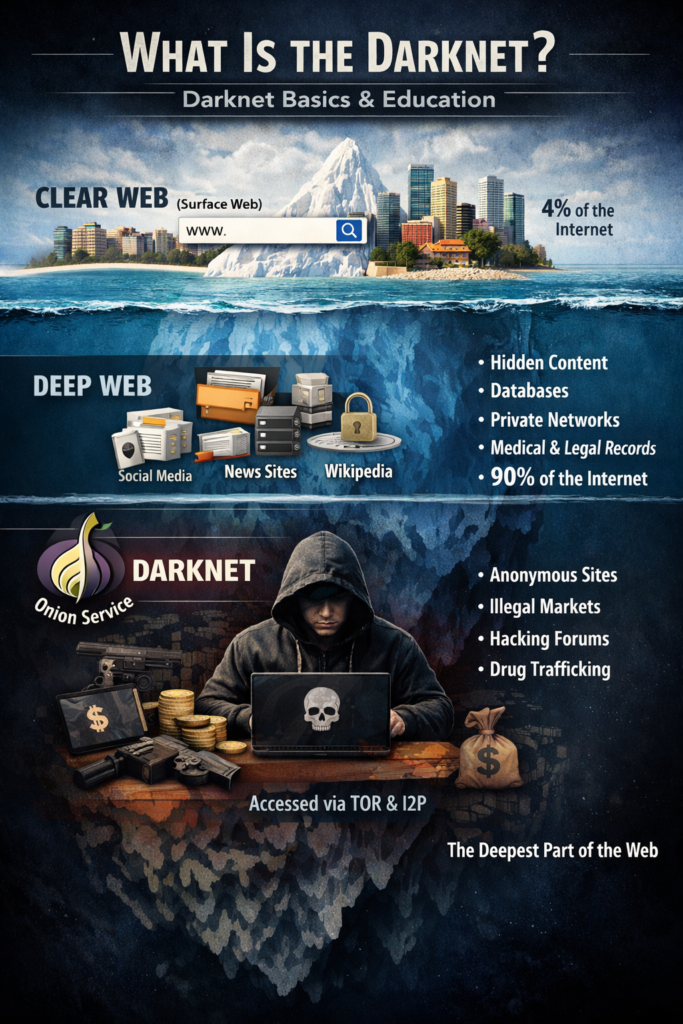
The darknet refers to a segment of the internet that is not indexed by traditional search engines and requires specific software to access. This hidden part of the web is often confused with the deep web, which encompasses all internet content that is not indexed by search engines, including benign elements such as online banking, private databases, and academic resources. In contrast, the darknet comprises intentionally hidden networks where anonymity is emphasized, making it distinct from both the surface web and deep web.
One of the defining characteristics of the darknet is its emphasis on anonymity. Users and service providers often utilize specialized software such as Tor (The Onion Router) to mask their IP addresses and encrypt their internet traffic. This anonymity draws a wide variety of users, including those seeking privacy for legitimate reasons, such as activists, journalists, and whistleblowers, as well as those engaged in illicit activities like drug trafficking and the sale of stolen data.
The technology underpinning the darknet relies on complex routing techniques and encryption to create layers of protection against surveillance. By routing data through multiple nodes all over the world, Tor ensures that users remain untraceable, which is a fundamental aspect of its architecture. This level of privacy and security makes the darknet a unique environment, fostering both constructive and detrimental uses. Many underground marketplaces operate on the darknet, showcasing goods and services that are often illegal or considered taboo in mainstream society. Nonetheless, the darknet is also a platform for free speech and is used by individuals in oppressive regimes seeking to communicate safely and freely.
Overall, the darknet is an intricate element of the internet, characterized by its distinctive anonymity, specialized technology, and dual nature, effectively serving both beneficial and illegal pursuits.
How to Access the Darknet
Accessing the darknet requires specific tools and a careful approach to ensure both safety and anonymity. The primary method for entering the darknet is through the Tor Browser, a specialized web browser designed to route internet connections through a network of servers, thereby masking the user’s IP address. To begin, download the Tor Browser from the official website to avoid malicious software. It is essential to verify the download against known checksums to ensure its integrity.
Using a Virtual Private Network (VPN) in conjunction with the Tor Browser is highly recommended. A VPN creates an additional layer of security by masking your real IP address from your internet service provider (ISP) and potential hackers. Select a reputable VPN service that prioritizes privacy and has a no-logs policy. This will help mitigate risks associated with accessing the darknet.
In addition to using the Tor Browser and a VPN, it is wise to adopt several best practices while navigating the darknet. Avoid revealing personal information, refrain from discussing identifiable details in forums, and be cautious about the websites you visit, as many contain illegal materials or scams. It is advisable to use virtual currencies, such as Bitcoin, for transactions, as they provide a degree of anonymity; however, it is crucial to understand how to use them safely.
While exploring, ensure that your device’s security settings are robust. Keeping your operating system and software updated can protect against vulnerabilities. Furthermore, utilize privacy-focused search engines tailored for the darknet to help find reliable resources without compromising your anonymity.
Finally, always be aware of the legal implications related to darknet activities. Familiarizing yourself with local laws can prevent unintended legal consequences, enabling a safer and more informed experience on the darknet.
Legal and Ethical Considerations
The darknet presents a unique mosaic of legal and ethical challenges that necessitate nuanced exploration. One must first acknowledge that the darknet is often associated with illegal activities, such as the trade of narcotics, weapons, and stolen data. These illicit undertakings create a complex legal landscape, as various jurisdictions grapple with the implications of enforcing laws that traditionally apply to the surface web. Law enforcement agencies worldwide strive to develop strategies to investigate and mitigate crimes linked to the darknet, often intersecting with privacy rights and considerations of free speech.
Beyond illegal activities, some segments of the darknet operate legally, devoted to protecting users’ privacy and fostering free expression in oppressive regimes. For instance, individuals may utilize anonymizing services for whistleblowing or engaging in political discourse without fear of reprisal. These legal facets challenge the binary perception of the darknet as solely a harbor for illicit behavior. Such distinctions unveil morally charged debates about censorship, the right to privacy, and the ethical implications of facilitating freedom of expression.
Furthermore, the ethical dilemmas surrounding the darknet are compounded by the potential for harm versus the necessity of privacy. Advocates for unrestricted access to information argue that the darknet serves as a crucial platform for dissenting voices. Conversely, critics express concern over the harm that can arise from the sale of illegal goods, thereby questioning the moral legitimacy of permitting such a space to thrive. Ultimately, navigating the legal and ethical dimensions of the darknet requires a delicate balance between upholding individual rights and ensuring public safety. The ongoing discourse around these issues reflects the ever-evolving nature of digital rights in our increasingly interconnected world.
The Future of the Darknet
The darknet, a realm of the internet often associated with anonymity and illicit activities, is anticipated to undergo significant transformations in the coming years. As regulatory measures increase globally, we may witness a bifurcation of the darknet into zones that cater to both privacy advocates and illegal practitioners. Stricter laws and enforcement may compel users on the darknet to adapt their practices, potentially leading to new forms of encryption and more sophisticated methods of data obfuscation.
Technological advancements such as artificial intelligence and machine learning are also poised to impact the darknet. These technologies can contribute both to the evolution of security measures used by darknet users and to the tools employed by law enforcement. Enhanced detection algorithms could be developed to trace and monitor darknet activities while, simultaneously, users may implement better anonymization techniques to maintain their privacy. This cat-and-mouse dynamic will fundamentally shape how the darknet operates in the coming decade.
Furthermore, the darknet’s future will likely be influenced by societal attitudes towards privacy and data security. The growing concern over digital surveillance has sparked debates about the importance of anonymous communication and safe spaces online. As more individuals seek refuge from invasive practices of data collection, the darknet may evolve as a platform for free speech and a bastion for those advocating for civil liberties. This shift presents critical implications for policy-making as lawmakers grapple with balancing the need for security and the preservation of freedom on the internet.
In conclusion, the future of the darknet is set to be shaped by a confluence of regulatory, technological, and societal factors. As these elements interact, they will not only redefine the darknet itself but will also influence broader conversations regarding privacy, security, and the ethical dimensions of our digital lives.